Security, Knowledge Graphs, and AWS PrivateLink

Get the latest in your inbox

Get the latest in your inbox
As mentioned in our April announcement about SOC2 Type II Certification, the Stardog Platform sits at the heart of modern data strategy in an enterprise. More enterprises are adopting a hybrid cloud approach with a combination of on-premises infrastructure and cloud resources. At Stardog, we prioritize performance and data protection, regardless of where and how it’s stored, in the development of our Enterprise Knowledge Graph platform.
This is why I’m excited that Stardog Cloud is the first Enterprise Knowledge Graph platform to support AWS PrivateLink. Stardog Cloud is able to securely access enterprise local sources and integrate them into your knowledge graph, further protecting critical and highly sensitive data in AWS. This means you can extend your data fabric to include all on-premise and cloud-based data sources with Stardog’s virtual graph.
Stardog Cloud uses an encrypted connection to securely connect to and query your locally hosted sources for some deployments. In some highly regulated environments, such as Life Sciences or Financial Services, there are additional layers of security around local data sources that make this approach difficult.
Now, by implementing AWS PrivateLink, Stardog Cloud is able to virtualize locally-hosted enterprise sources without sending data over the internet, instead relying on the private, secure connection provided by PrivateLink. This configuration also helps improve network performance. Since traffic bypasses the public internet, there is reduced latency and more predictable network performance.
AWS PrivateLink provides private connectivity between virtual private clouds (VPCs), supported AWS services, and your on-premises networks without exposing your traffic to the public internet. Interface VPC endpoints, powered by AWS PrivateLink, connect you to services hosted by AWS Partners and supported solutions available in the AWS Marketplace (source: https://aws.amazon.com/privatelink/).
To use AWS PrivateLink with Stardog, you must provision a VPC Endpoint Service in your AWS account. This service must be configured to point to AWS Network Load Balancer (NLB) as shown in the right side of Figure 1.
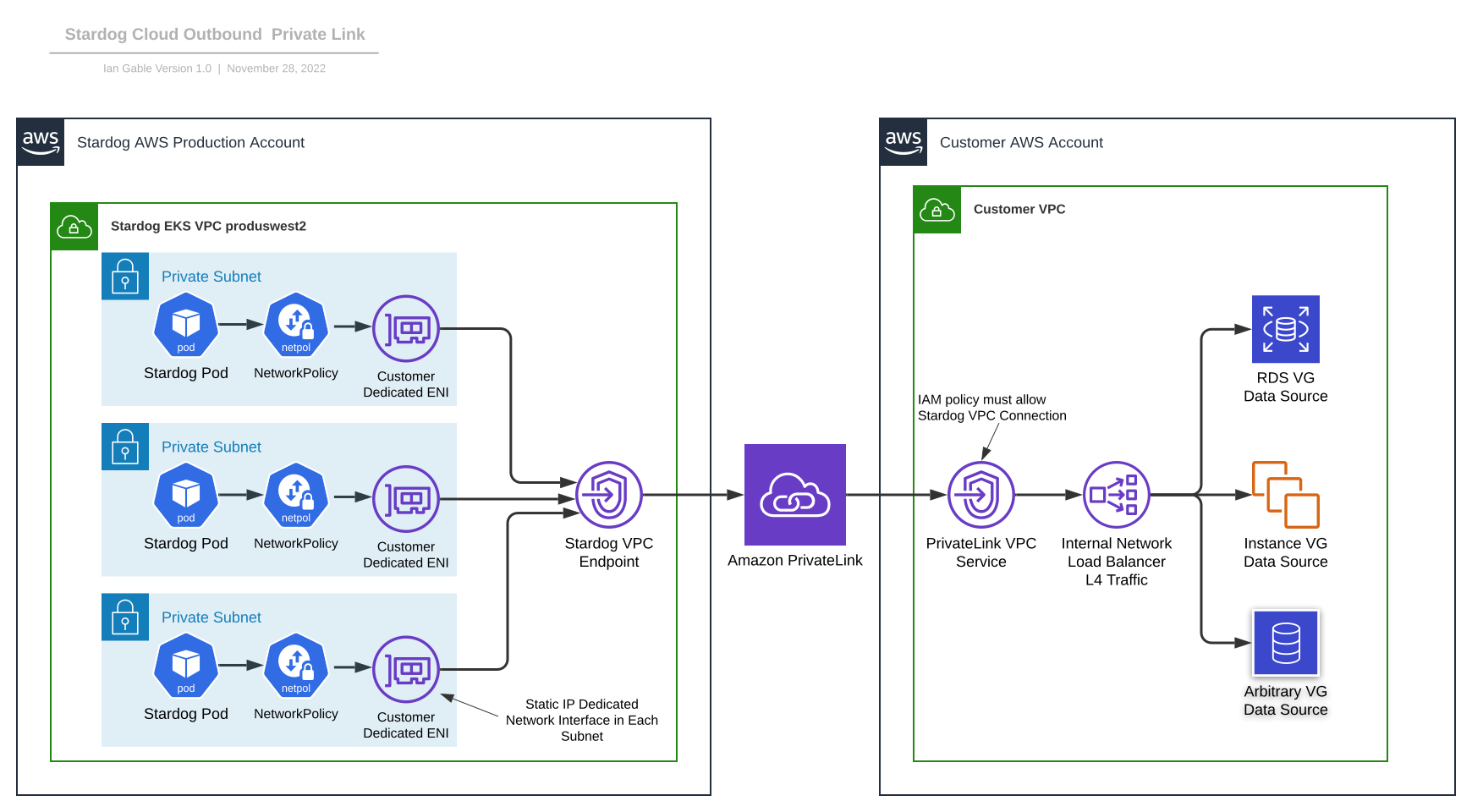
The NLB must then be configured to have a target group which points to a VG data source of interest. Neither the VPC Endpoint Service nor the NLB define a security group configuration; that means the security group associated with the VG data source must be configured to permit the traffic which originates from the NLB used to provide VPC Endpoint Service.
Origin IP preservation is not provided by PrivateLink; thus, all traffic appears to originate from your private NLB. In order to use a single NLB and VPC Endpoint Service to access multiple VG data sources, the NLB must be configured to accept traffic on multiple ports and forward that traffic to distinct target groups.
On the Stardog VPC side, we configure a VPC Interface Endpoint which creates dedicated Elastic Network Interfaces (ENI) inside each of the private subnets associated with the three availability zones in our production EKS environment (as shown on the left side of Figure 1).
Note that VPC Interface Endpoint is different than the VPC Endpoint Service, which is the AWS term for the receive side of the PrivateLink connection.
To protect each Customer Dedicated ENI, Kubernetes Network Security Policies are used to provide egress from the Stardog Pods associated with your VPC only to your dedicated ENIs. After the VPC Endpoint is provisioned, the IP addresses associated with those ENI remain static throughout the life of the provisioned interfaces which enables IP address-based Network Security Policy to be applied.
Support for AWS PrivateLink in Stardog Cloud is currently in Beta. If you are a current or potential Stardog Cloud customer and you have a use case that could benefit from PrivateLink support, please let us know, and we will help you get started.
How to Overcome a Major Enterprise Liability and Unleash Massive Potential
Download for free